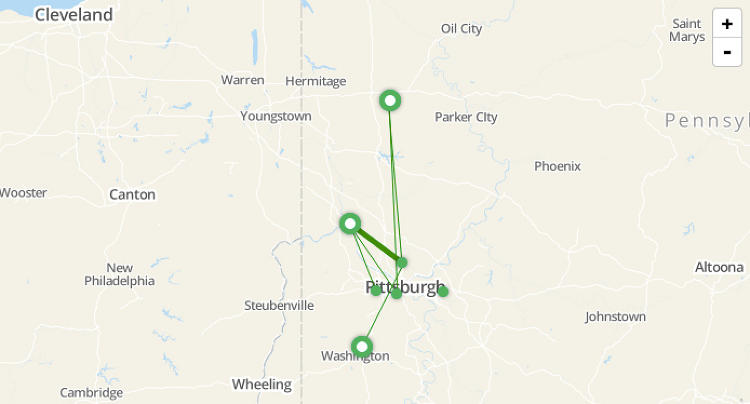
Figure 1 Identifying customers that visit multiple retail locations for the same store
(Source: Fast Company, “Here’s What Brick-And-Mortar Stores See When They Track You”)
Last week, the FTC announced a proposed settlement with Nomi Technologies, a retail tracking firm that monitors consumers’ movements through stores, for failing to adhere to their opt-out promises.
Nomi's Listen Service tracks consumers by monitoring the location of their devices as they move about. The approach does not identify an individual by name but instead monitors unique wireless identifiers emitted by the smartphones, wearables, and other wireless accessories that consumers carry.
The obscure nature of retail tracking technology has been somewhat controversial. On a number of occasions, retailers such as Nordstrom and Philz Coffee, and cities, such as the City of London, have discontinued its use once their consumers were made aware of the practice and expressed privacy concerns.
For context of consumer concern over this practice, a recent OpinionLab survey of 1,000 consumers indicated that, "8 out of 10 shoppers do not want stores to track their movements via smartphone" and "nearly half (43%) of shoppers are less likely to shop at a favorite retailer if the brand implements a tracking program."
The privacy issues are further exacerbated by the fact that most consumers are not aware that their device information may be captured as they walk by a store or visit an airport.
In light of the Commission’s proposed settlement with Nomi and the ongoing public debate, I thought it would be worthwhile to describe how different retail tracking technologies work, and in my opinion, the specific privacy trade-offs of each approach. My predecessor, Latanya Sweeney, has also blogged about this topic and the FTC held a seminar last spring, where I presented an overview on how some of this technology works.
OVERVIEW
Retail tracking generally works by monitoring individual's movements in or near locations of interest. The specific mechanisms can vary but often involve recording signals emanated by the individual or their devices as they move about.
For example, early retail analytics services relied on in-store cameras to optically record individual's movements (reflected “photon emanations” to be geeky) in order to count foot traffic or create heat maps of which product displays might be most popular. This technique was also a topic of discussion at an FTC workshop on facial recognition. Video retail analytics, while providing rich in-store patterns, typically does not employ facial recognition and therefore provides a somewhat higher degree of “practical obscurity” since it cannot identify consumers or link them across locations.
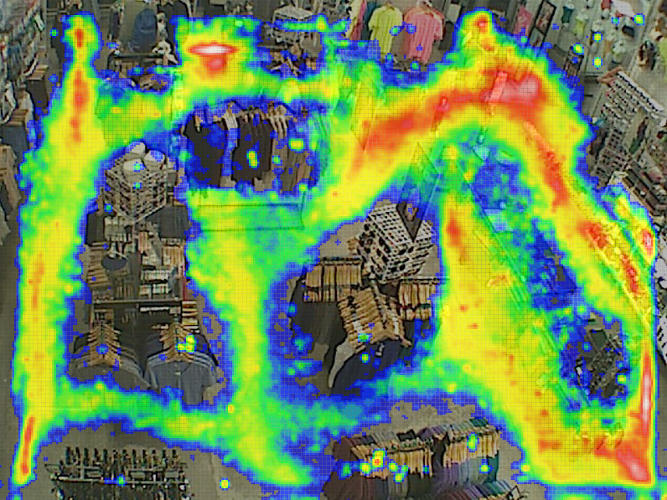
Figure 2 Example heatmap from a video based retail location system.
(Source: Here’s What Brick-And-Mortar Stores See When They Track You)
Newer approaches monitor signals broadcast from individual's devices as the device searches for or communicates with nearby devices and networks. This can consist of “active monitoring,” which is typically performed by the service the device is communicating with, such as by the cellular provider or by the WiFi hotspot the device is connected to. The other approach is 'passive monitoring', which intercepts signals from the device as it communicates or searches for other devices and networks.
For example, some passive retail analytics techniques intercept your communication to the cellular provider, or the beacons broadcast by your device as it searches for nearby WiFi hotspots. Most modern cellphones and wearables have an array of wireless antennas that regularly broadcast signals as they search for or communicate with cellular, WiFi, and Bluetooth networks – even when they are not in use. Note, the information collected is often referred to as “signaling information” in the header of the communication and distinguished from the actual contents which are typically not collected as this could potentially run afoul of wiretapping laws. It's also worth noting that other signals, including “Near Field Communication” (NFC), LED, and even acoustic signals, are used by retail analytics firms use to track individuals. However, I will limit the discussion to the most prominent.
By monitoring the strength of these signals and the associated identifier, the retailer is able to ascertain the volume of visitors to their store, the frequency with which visitors return, the behavior of passers-by, or even the demographics of visitors to a particular location (as in the case of carrier-provided retail analytics).
The privacy concerns will ultimately be impacted by the identifier used (i.e., how persistent it is or the effectiveness of obfuscation), consumer awareness (or notice), and availability of choice or “opt-out” mechanisms, which I lay out below.
IDENTIFIERS
Retail analytics firms track these signals and associated identifier(s) in order to triangulate and record the location of an individual device. As such, the identifiers themselves can vary and present different privacy concerns.
Active monitoring by your cellular carrier is often based on persistent identifiers associated to your mobile devices – which can include your International Mobile Station Equipment Identity (IMEI), International Mobile Subscriber Identity (IMSI), or Mobile Station ISDN (MSISDN), which is assigned when you purchase your device and SIM card. The carrier relies on these numbers to provide service and can also use them to generate aggregate analytics to retailers.
In contrast, passive cellular tracking techniques utilizes Temporary Mobile Subscriber Identifiers (TMSI) that are assigned by the carrier but rotate over the course of period of hours to weeks, depending on the configuration of the cellular network. Use of this identifier inherently provides some privacy protections over hardware identifiers since the rotating identifier limits the amount of time an individual's behavior can be linked. For example, repeat visits over the course of the week can be tied back to the same individual, but not over the course of a month or a year. Technology to passively track persistent cellular identifiers such as IMSI is also readily available (known as “IMSI catchers”), however, to my knowledge, its use has primarily been limited to law enforcement uses.
Similarly, hardware identifiers such as WiFi or Bluetooth Media Access Control (MAC) addresses are persistent throughout the life of the device since they are tied to the physical embedded chipsets. As part of the wireless protocol(s), these identifiers are automatically broadcast when devices search for networks or communicate with other devices, including wireless access points, wireless headsets, and health trackers -- so they are visible to a broader set of observers.
This persistent identifiers often can be linked to individuals by name. For example, when you sign into a commercial WiFi hotspot, your MAC address is tied to the information you use to sign up for the service. Additionally, automatic WiFi probes also broadcast the names of last networks a device has connected to, which potentially reveal additional information about the individual, such as the name of their home or work network (i.e., “FTC Wireless”). This information could allow observers to link a MAC address to a given user or network, but it is unclear whether any companies collect or use this information.
Finally, in the case of smartphones, apps and advertisers sometimes rely on MAC addresses as a mechanism to uniquely track behavior online -- thereby providing a mechanism for linking offline (physical) and online behavior.
As a result of sensitivities associated with hardware identifiers, some smartphone manufacturers have attempted to build in features which limit retail tracking by randomizing the device's wireless identifier (MAC address) when the device is not in use, although its effectiveness is somewhat limited. The Internet Engineering Task Force (an internet standards body) is also experimenting with ways to improve smartphone privacy by randomizing MAC address.
Some retail analytics providers, including Nomi, cryptographically hash the identifier prior to retention in an attempt to reduce some of the privacy concerns. This “hashing” attempts to obfuscate the original identifier (such as MAC address) while still providing a unique string which can be used to identify the device over time and space. As stated in the FTC’s complaint:
“Nomi cryptographically hashes the MAC addresses it observes prior to storing them on its servers. Hashing obfuscates the MAC address, but the result is still a persistent unique identifier for that mobile device. Each time a MAC address is run through the same hash function, the resulting identifier will be the same. For example, if MAC address 1A:2B:3C:4D:5E:6F is run through Nomi’s hash function on ten different occasions, the resulting identifier will be the same each time. As a result, while Nomi does not store the MAC address, it does store a persistent unique identifier for each mobile device. Nomi collected information about approximately nine million unique mobile devices between January 2013 and September 2013.”
However, hashing is also of limited effectiveness as described in the majority statement:
“Although Nomi took steps to obscure the MAC addresses it collected by cryptographically hashing them, hashing generates a unique number that can be used to identify a device throughout its lifetime and is a process that can easily be “reversed” to reveal the original MAC address. See, e.g., Jonathan Mayer, Questionable Crypto in Retail Analytics, March 19, 2014, http://webpolicy.org/2014/03/19/questionable-crypto-in-retail-analytics/ (describing successful efforts in “reversing the hash” to identify the original MAC address).”
Essentially, while hashing attempts to remove some of the risk associated with use of a persistent hardware identifier, it is often easy to circumvent. In fact, free precomputed tables of known hashes (rainbow tables) are available that make reversing known hashes practically instantaneous.
In addition, even hashed, the use of a persistent identifier presents privacy issues since tracking pattern of movement in itself is often enough to uniquely identify an individual. As this technology becomes more widespread, a single retail analytics firm that services multiple retail chains will be able to collect a large pattern of individual’s movements, even if the information is not shared between unaffiliated chains.
NOTICE
These various approaches also vary to the degree of notice that is offered to consumers.
For the active forms of tracking, consumers are typically given notice when first signing up to the service, such as in the case of purchasing cellular service or logging into a commercial WiFi hotspot. In the case of iBeacons, consumers typically enable a feature on their phone or download an app which does the “tracking.” (Note: in the case of active Bluetooth monitoring via iBeacons, it’s actually the consumer’s phone that “tracks” the retail location and sends information back to the retail provider.)
However, many of the non-active techniques passively record signals so there's technically no way to detect and be made aware of the activity without signage to that effect. One industry self-regulatory group’s code of conduct requires retail analytics firms to "take reasonable steps to require that companies using their technology display, in a conspicuous location, signage that informs consumers about the collection and use of MLA Data at that location." However, not all retail analytics companies adhere to these principles, nor do any of the retailers that would be responsible for implementing in-store signage, making the notice essentially voluntary.
Finally, wireless signals are typically not constrained by store walls so visitors driving by or visiting a neighboring store will likely not be aware of the presence of retail location tracking in neighboring stores. Similarly, signage will have similar limitations for retail location techniques utilizing drones.
CHOICE
Some of the retail analytics techniques are opt-in, such as iBeacon and location enabled shopping apps. However, the passive techniques typically operate under an opt-out regime, as do the carrier-based methods.
Once consumers are made aware, some of the firms allow the consumers to opt-out. For example, AT&T and Verizon provide dashboards by which consumers can manage their privacy preferences and opt out of having their location information used for marketing purposes.
Mobile analytics companies that rely on passive WiFi tracking technologies and adhere to the smart-places principles allow users to opt out by entering their MAC address into the Smart Places opt-out form. However, the principles do not allow individuals to opt-out from data collection for the purpose of network management or security.
With the exception of turning off their devices or putting them into “airplane” mode, there is currently no way to avoid collection altogether since opt-out processing typically occurs during retention. That is, sensors or carriers still collect consumer’s activities at the point of interest, then process the opt-out before being stored on their backend systems.
Personal health trackers and other wearables typically do not have an easy way to identify their MAC address and some do not have “Off” buttons, which constrains consumers’ ability to limit tracking of these devices.
ANALYSIS
| IDENTIFIER | NOTICE | CHOICE | |
| In-store Camera | None [1] | Signage optional | None |
| Active Cellular | Persistent (IMEI/IMSI/MSISDN) | Typically provided during Carrier Signup | opt-out via carrier |
| Passive Cellular | Temporary (TMSI [2]) | Signage optional [3] | None |
| Active WiFi | Persistent (WiFi MAC) | Typically provided during WiFi sign-up | NA / opt-in (based on hotspot terms) |
| Passive WiFi | Persistent (WiFi MAC) | Signage optional [3] | Smart-places.org for participating MLAs [4] |
| Active Bluetooth | Varies based on app and OS features | Notice provided during app install | opt-in |
| Passive Bluetooth | Persistent (BT MAC) | Signage optional [3] | Smart-places.org for participating MLAs [4] |
| 1 - This excludes facial recognition, which at the present time is not in use for retail tracking | |||
| 2 - Based on statements from Path Intelligence CEO, a MLA- utilizing passive cellular | |||
| 3 - Mobile analytics providers must “take steps” -- but not strictly required. Neighboring stores and sidewalks limited. | |||
| 4 - Opt-out for wearables and other accessories limited | |||
Retail tracking has many benefits for retailers and consumers alike. Stores are able to better understand the behaviors and preferences of their shoppers, and individuals are in turn, receive better service. However, the technology does present privacy trade-offs.
I’ve attempted to highlight some of the trade-offs of the various mobile retail tracking techniques. Given the variety of approaches, there are a number of things that industry could do to alleviate the privacy concerns and address some of the gaps in consumer awareness.
For example, at the FTC’s 2013 seminar on mobile device tracking, I suggested that passive retail analytics technology devices could automatically broadcast standardized, semi-continuous wireless signals that announce their presence as a technical solution to pervasive computing in the public sphere. One could imagine open WiFi or Bluetooth networks which alert users to the existence of mobile retail tracking and allow them to temporarily join in order to opt-out. Additionally, industry or individuals could develop privacy enhancing apps that allow privacy conscious users to automatically disable transmission of signals when approaching these networks in order to avoid collection altogether.
There are also additional technical measures that could provide additional privacy protections for identifiers, such as hashing the incoming identifiers at the time of capture with rotating salts based on time or retail location. This would provide protections similar to the TMSI, which prevents linking activity to the same device over long periods of time or across multiple locations (in the case of the location-based salt).
These are just some of the potential ways to evaluate and address the trade-offs with this emerging technology.
